Holiday season is a good time to train your users about common security risks they may fall into it. Let me describe how to create a security awareness campaign and how to let users know their score.
In Microsoft’s latest Digital Defense Report 2022 there are some very good conclusions and suggestions how to improve security in the digital space. In an environment where a lot of false information is publishes, phishing gets better and better. And people still need to be aware about security in their digital environment. The numbers, Microsoft can provide, are impressive:
- 43 trillion signals synthesized daily
- 70 billion threats blocked in 2021
- 10,000 domains removed, used by cybercriminals and 600 used by nation state actors
- 8,500+ security and threat intelligence experts across 77 countries
We just cannot rely on Microsoft alone when it comes to protection against threats. We also need to onboard our users and keep them trained and aware about security. An excellent approach to that is a security awareness campaign and what could be the best time to do that during holiday season!
Create your own security awareness campaign
Within the security center you can create your very own security awareness campaign. In the left navigation you can launch the Attack simulation training, With those trainings you are able to run realistic attack scenarios in your organization. These simulated attacks can help you to improve security awareness in your organization.
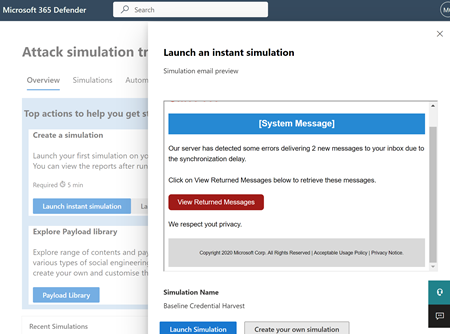
From here you can start a couple of simulations. The easiest way to learn how it works is with an assisted simulation which can be targeted against a couple of users first. This simulation is looking for credentials and very easy to create.
If you are ready for your own simulation you can create and chose among a couple of simulations:
- Credential Harvest: In this type of technique, a malicious actor creates a message, with a URL in the message. When the target clicks on the URL within the message, they are taken to a website, the website often shows input boxes for luring the target to submit their username and password. Typically, the page attempting to lure the target will be themed to represent a well-known website to build trust in the target.
- Malware attachment: In this type of technique, a malicious actor creates a message, with an attachment added to the message. When the target opens the attachment, typically some arbitrary code such as a macro will execute in order to help the attacker install additional code on a target's device, or further entrench themselves.
- Link in attachment: In this type of technique, which is a hybrid of a Credential Harvest, a malicious actor creates a message, with a URL in an attachment, and then inserts the attachment into the message. When the target opens the attachment, they are represented with a URL in the actual attachment, if the target then clicks on that URL they are taken to a web site, the website often shows input boxes for luring the target to submit their username and password. Typically, the page attempting to lure the target will be themed to represent a well-known web page to build trust in the target.
- Link to malware: In this type of technique, a malicious actor creates a message, with an attachment added to the message. However instead of directly inserting the attachment into the message, the malicious actor will host the attachment on a well-known file sharing site, (such as SharePoint, or Dropbox) and insert the URL to the attachment file path into the message. When the target clicks on the URL it will open the attachment, typically some arbitrary code such as a macro will execute in order to help the attacker install additional code on a target's device, or further entrench themselves.
- Drive-by url: In this type of technique, a malicious actor creates a message, with a URL in the message. When the target clicks on the URL within the message, they are taken to a website, the site will then try and run some background code to gather information about the target or deploy arbitrary code to their device. Typically, the website attempting to lure the target will be a well-known website that has been compromised in some fashion, or a clone of a well-known website itself. This familiarity with the website builds trust in the target that it is safe to click, this is also sometimes known as a watering hole technique.
- OAuth consent grant: In this type of technique, a malicious actor has created an Azure Application that asks the target to grant the application permissions over some of the target's data. The application will provide a URL that is send to the target by malicious actor along the similar lines of a credential harvest technique, as a URL in a message. This time, clicking on the URL will activate the applications consent grant mechanism, displaying a message such as "Contoso App, would like read access to your inbox" please click the button to approve or deny the request.
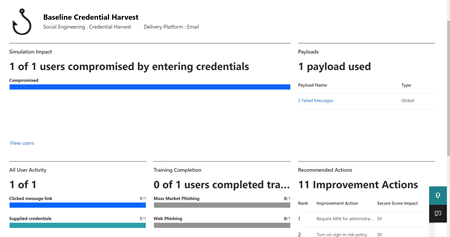
For the simulation to be as realistic as possible think about something reliable within your organization and include that to the message. If you start with credential harvest you can create user trainings afterwards that supports users to pay more attention to those types of attacks. The assistant will drive you through the necessary steps to create a successful campaign. What is really useful that you can assign simulations in different languages and you can also assign trainings to the users if they fail the simulation. After the simulation was finished you will get a summary report how the campaign went. This is especially useful when you repeat those types of simulations after a while.
Learn more: Get started using Attack simulation training - Office 365 | Microsoft Learn
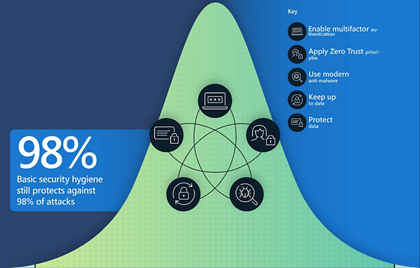
98% basic security hygiene still protects against 98% of attacks
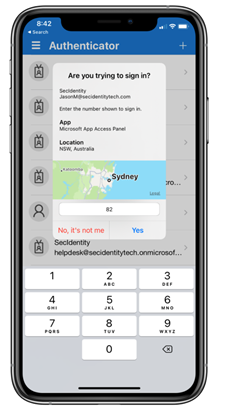
Be aware that basic security hygiene can help you to prevent threats in your organization. Multifactor authentication is the easiest to use and still a big struggle for organizations. To prevent against MFA fatigue, Microsoft will change MFA authentication to Authenticator number matching.
The Cyber resilience bell curve infographic shows basic security hygiene practices to implement to protect against 98% of attacks:
- Enable multifactor authentication,
- apply zero trust principles,
- use modern anti-malware,
- keep up to date,
- and protect data.
The attack simulation is a great way to improve user awareness!